Cyber threats are more sophisticated and prevalent than ever before. To safeguard their valuable data and maintain customer trust, companies must employ robust security measures. One essential strategy in the fight against cybercrime is external penetration testing. But what exactly…
Blog

Introduction to the FTC Safeguard RuleThe Federal Trade Commission (FTC) Safeguard Rule, a crucial part of the Gramm-Leach-Bliley Act (GLBA), aims to ensure financial institutions protect consumer information. Initially established in 2003 and amended in 2021, the rule requires these…
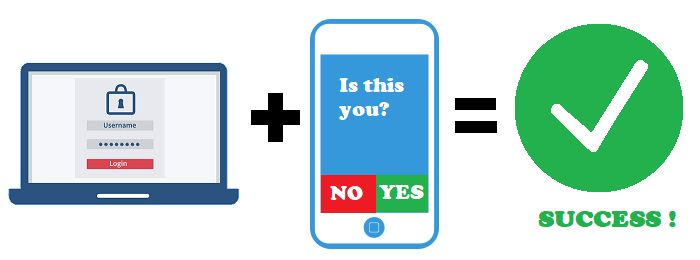
Use Multi-Factor Authentication (MFA) Description Multi-factor authentication (MFA) adds an extra layer of security to your accounts by requiring multiple forms of verification before granting access. This significantly enhances your account's security by making it more difficult for unauthorized individuals…

DescriptionStaying informed about cybersecurity threats and best practices is crucial in today's digital landscape. Educating yourself about potential risks, common attack methods, and effective security measures empowers you to better protect your personal and professional digital assets from cyber threats.Why…

DescriptionPublic Wi-Fi networks are often insecure and vulnerable to cyber attacks, making them risky for conducting sensitive transactions such as online banking or shopping. Avoiding public Wi-Fi for these activities helps protect your personal and financial information from being intercepted…

Backup your Data Regulary DescriptionRegular data backups are essential for protecting your important files and ensuring their availability in case of accidental deletion, hardware failure, or cyber-attacks like ransomware. Backing up your data regularly helps minimize the risk of data…

Secure Your Wi-Fi Network DescriptionSecuring your Wi-Fi network is essential to prevent unauthorized access to your internet connection and connected devices. A secure Wi-Fi network helps protect your personal and sensitive data from being intercepted or compromised by cybercriminals.Why It's…
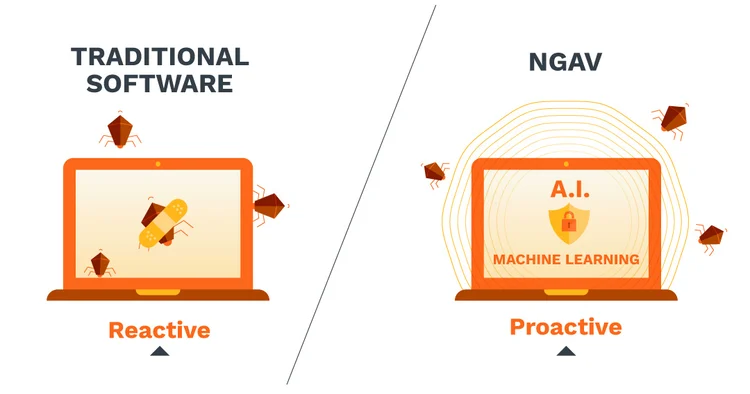
DescriptionNextGen AV and Endpoint Detection and Response (EDR) software is a crucial component of cybersecurity that helps detect, prevent, and remove malicious software (malware) from your computer or device. It works by scanning files and programs for known patterns or…

Use a Firewall – Tip of the Day April 15, 2024 DescriptionA firewall is a network security device or software application that monitors and controls incoming and outgoing network traffic based on predetermined security rules. It is a barrier between…

Beware of Phishing ScamsDescriptionPhishing scams are deceptive attempts by cybercriminals to trick individuals into revealing sensitive information such as passwords, usernames, credit card numbers, or other personal data. These scams often come in emails, text messages, or phone calls that…
Recent Comments
Recent News
-

10 SURPRISING CYBER SECURITY STATISTICS
May 9, 2022 -

SOCLOGIX NAMED TO MSSP ALERT’S TOP…
May 9, 2022 -

Barbarians at the Gate? Cyber security…
September 13, 2022
Category
- Biggest (1)
- Business (4)
- Checklists (4)
- Cybersecurity (14)
- News (6)
- Tip of the Day (10)
- Uncategorized (2)
Popular Tag
Let's Work Together
Protect your business with SOClogix's expert cybersecurity solutions.

